From the mailbag:
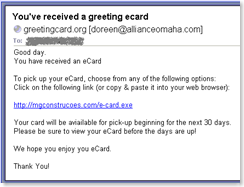
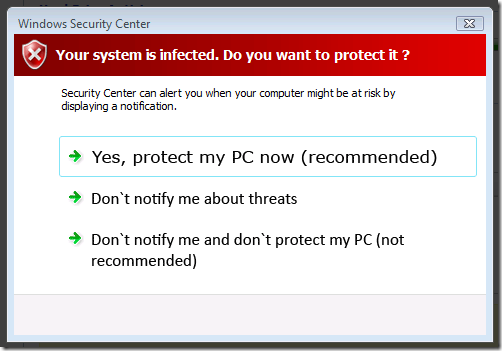
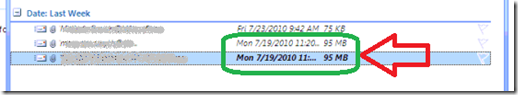
“After a migration, some of the users showed up in the SBS Console with a key under their name and some didn’t. Example:


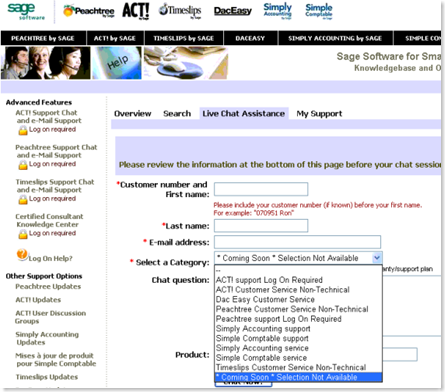
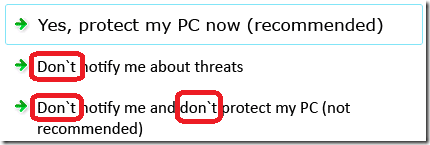
I can’t change RWW access for these users either – it’s grayed out:
or even…
What does that key mean and how do I get rid of it?
ANSWER
The key means the users are domain administrators, and therefore you can’t disable RWW for them individually. Don’t be fooled by the “User Role” column.
The key can come from two places.
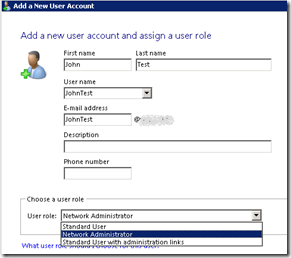
1 – If a new user is created with the User Role of Network Administrator when running the SBS 2008 Add a new user account wizard, they get that key.
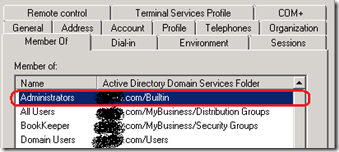
2 – In a migration scenario (like this one) if a user was a member of the “Administrators – domain/Builtin” Security Group on the source server, they will show up with that key after the migration to the SBS 2008 box (see George McFly above):
Before we move onto the resolution (below), there are a few points to remember with User Roles in SBS 2008 detailed below. The wizards make it VERY easy to blow stuff up accidentally.
CAUTION – It is highly recommended that you read understand all of the information in this blog post before making changes any to user accounts and groups. There is no Undo or Recycle Bin for Active Directory changes in SBS 2008 RTM.
BACKGROUND INFO ON USER ROLES
When running the “Add a new user account” wizard in SBS 2008, you have
(by default) three options for User Roles:
- Standard User
- Network Administrator
- Standard User with Administration links
Here’s what you get with each role.
Default group memberships by User Role:
|
Default SBS 2008 Groups & User Roles
|
Standard
User
|
Standard User
w/ Admin Links
|
Network
Administrator
|
| All Users* |
Yes
|
Yes
|
Yes
|
| Windows SBS Fax Users |
Yes
|
Yes
|
Yes
|
| Windows SBS Link Users |
Yes
|
Yes
|
Yes
|
| Windows SBS Remote Web Workplace Users |
Yes
|
Yes
|
Yes
|
| Windows SBS SharePoint_MembersGroup |
Yes
|
Yes
|
No
|
| Windows SBS Admin Tools Group |
|
Yes
|
Yes
|
| Windows SBS Administrators* |
|
Yes
|
Yes
|
| Windows SBS Fax Administrators |
|
|
Yes
|
| Window SBS SharePoint_OwnersGroup |
|
|
Yes
|
| Windows SBS Virtual Private Network Users |
|
|
Yes
|
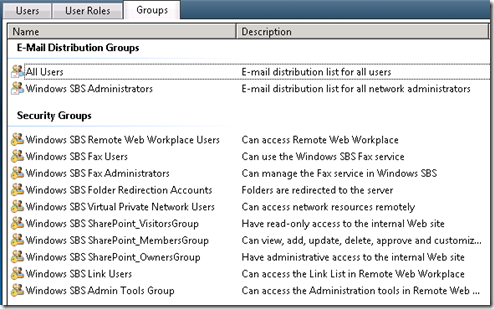
HINT: *The All Users and Windows SBS Administrators groups are E-mail Distribution Groups, not security groups, which means that you can’t assign security permissions to those groups.
Normally you would think that a group named “Windows SBS Administrators” would be some type of security group, but that’s just one of the gotchas in SBS 2008. The Groups tab in the SBS 2008 console makes this easy to see, but if you’re poking around in AD, you might forget. Just look for the ‘key’ icon to differentiate E-Mail and Security Groups.
So, this begs the question, “If I create a standard user, right-click them in the console and make them a member of all of the same groups as the Network Administrator in the chart above, do they get the ‘key’ icon?
Answer: No. You have to use Change user role for user accounts wizard (or dig into AD).
IMPORTANT USER ROLE / USER ACCOUNT TIPS
Things to remember about User Roles and user accounts in SBS 2008:
- NEW USERS – User Roles are chosen at the time the User Account is created if you use the “Add a new user account” wizard (shown above).
- CUSTOM ROLES – Have you ever gotten a call like this, “Mary is moving to part time, and we hired another person to do the same job in the afternoon – can you setup a new user account for Jennifer with the same permissions?”
Now you can create a new role like “Reception” and create it based on Mary’s current permissions / memberships. This is great if you start creating new roles like “Warehouse”, “Intern”, “Vendor”, etc.
- CHANGES – You can change the User Role assigned to an existing user after the fact using the “Change user role for user accounts” wizard (shown below).
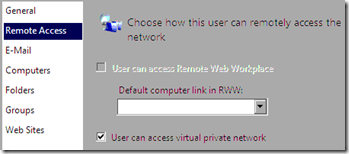
- APPLYING ROLES – When applying a “User Role” to an existing user, you are given the option of adding or replacing the existing user permissions (shown below). This is where it gets sticky.
- ADJUSTING PERMISSIONS OUTSIDE THE USER ROLE – After a User Role has been applied, you can tweak the permissions. This is great for creating department supervisors after the department has been mapped out.
Example – You create a custom “Sales Rep” User Role, and then apply it to all sales users, including Marty McFly. Afterwards, since Marty is actually the Sales Manager, you also give him access to financial data.
- REPLACE VS. ADD – If you re-apply a User Role to a user, you can accidentally remove any customizations to them. This is where you break the step above.
Example – The custom “Sales Rep” user role has recently been updated to include a new e-mail distribution list. Then you decide to re-apply the permissions to Marty. Congratulations. You just took away Marty’s access to the financial data and made him a normal Sales Rep drone, and not a manger.
- TRUST BUT VERIFY – Just because you see an entry in the “User Role” column, don’t assume that the user has had no customizations made to their account.
- WE DON’T NEED NO STINKING WIZARDS – If you’re old school and manually create a user in Active Directory Users and Computers instead of the SBS Console, the user won’t show up in the SBS Users Console.
Why? Because the attribute of “msSBSCreationState” = “<not set>”.
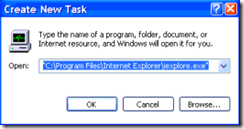
But, you can change this in Active Directory by setting that to “Created”. Example – User account that will not show up in the SBS 2008 console: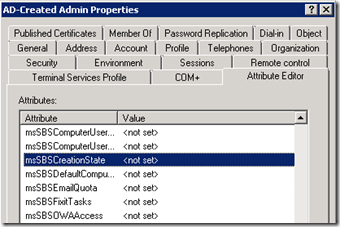
Example – User account that will show up in the SBS 2008 console: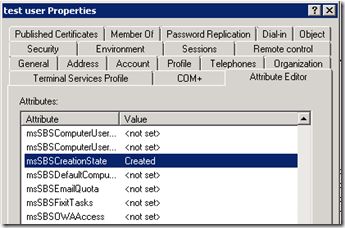
RESOLUTION
OK, you understand the difference between Add & Replace, and the implications of re-applying a user role to an individual.
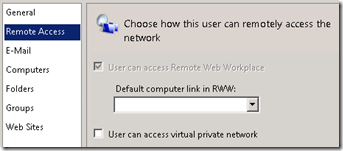
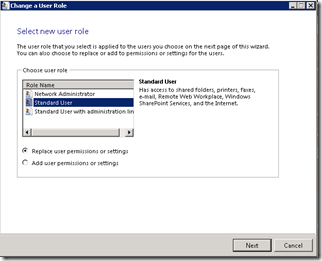
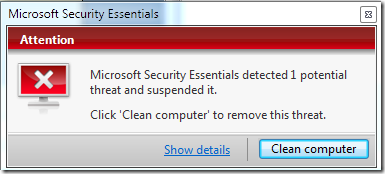
After you make a copy of the user group membership settings (because you love your job) you need to apply the “Standard User” User Role to that user and choose “Replace user permissions or settings” to get rid of that domain admin key.
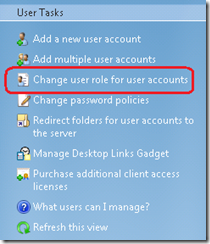
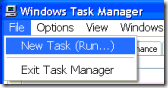
- Open the SBS Console, click Users and Groups, then click the Users tab.
- Click “Change user role for user for user accounts” wizard on the right.
- Select the role for the user account (in our case Standard User), choose “Replace user permissions or settings”, and click Next.
- Click on the name of the user on the left from the “All user accounts” column, click the Add button to move their name to the right column, then click the “Change user role” button.
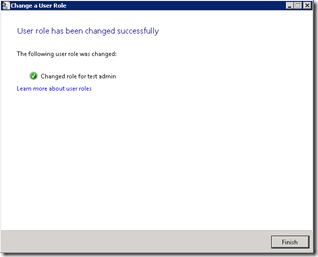
- Done. Click Finish.
ALTERNATE METHOD
If you’re AD savvy you can always open Active Directory Users and Computers and remove membership the ‘Administrators – domain/Builtin’ Security Group. This just takes away the ‘Administrator’ permissions and leaves everything else in tact.
Props: Thanks to Cory Rammer, MCSA/MCSE and all-around nice guy for his help on this post!
VN:F [1.9.20_1166]
Rating: 0.0/10 (0 votes cast)




 I was customizing a new
I was customizing a new