Just because a port is open in RRAS or ISA (circa SBS 2003) doesn’t mean that it isn’t being blocked elsewhere, like at the ISP or because port forwarding isn’t setup properly in your firewall. Sometimes you need an outside view of the external ports on your internet connection.
DISCLAIMER – Only open the ports you absolutely MUST have. Example, if you’re not running the POP3 connector or FTP, don’t open those ports! If you’re not sure about a port, check the Port/IP Lookup on Sans.org or ask someone who knows!
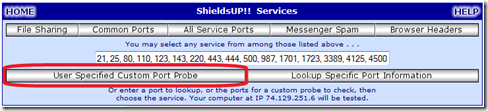
To check all of the commonly used SBS ports at once:
- Go to www.grc.com/default.htm
- Scroll down & click ShieldsUP!
- Click Proceed
- In the center box on that page, paste this string:
21, 25, 80, 110, 123, 143, 220, 443, 444, 500, 987, 1701, 1723, 3389, 4125, 4500
- Click User Specified Custom Port Probe
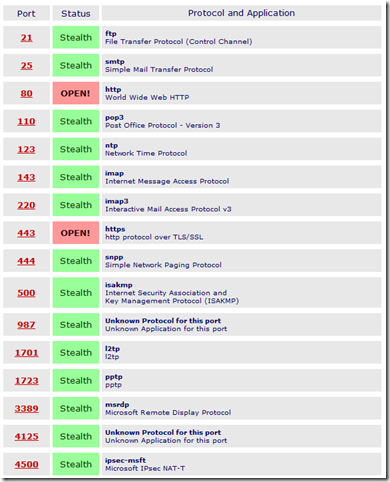
This scan will come back with a list of ports you entered and show the status.
Below is a handy chart that I stole from Susan and Windows IT Pro and updated a couple of times over the years.
Common Ports for Small Business Server (SBS)
|
TCP Port |
Service |
Description |
|
21 |
FTP |
Enables external and internal file transfer |
|
25** |
SMTP – Exchange |
Enables incoming and outgoing Simple Mail Transfer Protocol (SMTP) mail for your Exchange Server |
|
80 |
HTTP – IIS |
Enables all nonsecure browser access, including: internal access to IIS Webs including the https://livecasinogo.ca/ company Web, Windows SharePoint Web, Windows SharePoint administration Web, and server monitoring and usage reports Enables internal access to Exchange by OWA and OMA clients (SBS 2003) |
|
110 |
Enables Exchange to accept incoming Post Office Protocol (POP3) mail | |
|
123 |
NTP |
Enables the system to synchronize time with an external Network Time Protocol (NTP) server |
|
143 |
Enables Exchange to accept incoming Internet Message Access Protocol v4 IMAP4-compliant messages | |
|
220 |
Enables Exchange to accept incoming Interactive Mail Access Protocol v3 IMAP3-compliant messages | |
|
443** |
HTTPS – OWA, OMA, Outlook Anywhere, & RWW |
Enables all secure browser access, including external access to Exchange for Outlook 2003/2007, OMA and OWA; required for external access to server monitoring, usage reports and RWW (SBS 2008). OMA has been deprecated from SBS 2008. See SBS 2008 RWW video here. |
|
444 |
WSS (SBS 2003) |
Enables internal and external access to Windows SharePoint Services (WSS) Companyweb (SBS 2003) |
|
500 |
IPSec |
Enables external VPN connections by using IPSec |
|
987** |
WSS (SBS 2008) |
This Secure Hypertext Transfer Protocol (HTTPS) port makes Windows SharePoint Services (WSS) Companyweb site viewable through Remote Web Workplace (SBS 2008). See SBS 2008 RWW video here. |
|
1701 |
Enables external L2TP VPN connections | |
|
1723 |
Enables external PPTP VPN connections | |
|
3389*** |
Enables internal and external Terminal Services client connections (see Note below) | |
|
4125 (Note: you can change this port in RRAS) |
Enables external OWA access to Exchange, plus internal and external HTTPS access to the client Web site (SBS 2003) | |
|
4500 |
IPSec |
Internet Key Exchange (IKE) Network Address Translation (NAT) traversal |
**Note: The ports listed above in bold are required by SBS 2008, per Microsoft TechNet article “Managing Windows Small Business Server 2008 Remote Web Workplace”, including port 3389, but see article below.
***Question: Should I open port 3389 for remote administration or remote desktop connections?
Answer from Microsoft: “You no longer need to open port 3389. Windows Small Business Server 2008 uses Terminal Services Gateway to redirect traffic from port 443 to a selected desktop or server for RDP connections. You would need to use RWW or configure the Terminal Services client to use TS Gateway.”
Source: http://technet.microsoft.com/en-us/sbs/cc817589.aspx
There’s also a post on the Official SBS Blog that talks about an IPSec issue back in 2008 that affected ports 1645-1646, 1701, 1812-1813, 2883 & 4500.
I’ll try to keep this form updated as time goes on and will keep a permanent copy at http://www.nogeekleftbehind.com/sbs-ports/.