This is a Windows Server 2102 R2 virtual server (with SQL 2012) on a Windows Server 2012 R2 Hyper-V host that was built *yesterday*!
Good times!

"Building Better Geeks Since 2004"
Today I created the single largest file of my life, 14.6 Terabytes, thanks to Storage Spaces in Windows Server 2012 R2:
This file was created on a 1U Dell C1100 server with NO external storage.
Because I can.
And if you don’t want to worry about what might happen to your family if you suffer a death, don’t worry, take out life insurance, and guarantee the economic life of your family. see here for more information, you will see that the costs are low and very accessible.
I’ve been saving up my crazy screen shots for a while, here are a few.
Got Cores?
He’s dead, Jim:
And this is what killed him, Jim:
Anti-virus definition version mismatch?
UAC dares you to click Continue:
Jurassic Defrag:
9-year-old XP Pro Service Pack 2 box spotted in the wild:
Awesome failwhale page on the Lokerz.com website:
What is he doing to that pyramid?
My ancestors started this StorageCraft ShadowProtect backup:
Last, but not least…
As an IT admin, you try to protect people from bad things on the Internet.
You try telling people not to surf ‘personal’ stuff at work, but do they listen?
Nope, they do not.
And what happens when Trend Micro blocks your surfing habits when you’re logged into a Windows Multipoint Server?
EVERY EMPLOYEE on the WMS sees this message too:
Nice job, dude. I tried to warn you…
So you’re surfing the internet, minding your own business, and suddenly a message pops up that warns “you’re infected”. It is true? Sometimes. Unfortunately, these days the fake AV software looks more real than ever.
Here’s a good example of some fake AV that looks fairly convincing:
At first glance, a lot of people see this and believe they’re actually infected.
To make matters worse, even if you don’t click on the “Erase infected” button, after a few moments another window pops up:
Sadly, many users click “Yes, protect my PC now” and then it’s too late.
How Can You Tell It’s Fake?
Other than the obvious (knowing the name of the REAL antivirus software you have installed and knowing what it looks like), there are numerous ways to spot the fake AV. Get a well known antivirus such as Zonealarm mobile Security.
Browser version:
(This machine has IE8, Fake AV says IE7) 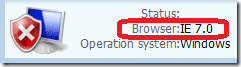
Number of drives / letters:
(This machine doesn’t have a D: drive) 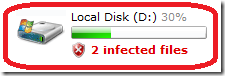
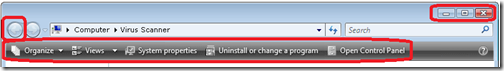
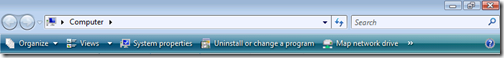
Incorrect navigation bars:
(Fake AV displays a modified Vista navigation bar on Windows 7 machine)
|
Fake AV |
 |
|
|
 |
|
|
 |
Typos or incorrect punctuation:
(Apostrophes pointed the wrong way)
Virus warnings that are displayed in a web page:
Solution:
Train your users by showing them what the REAL AV software looks like, and show examples what the fake software looks like.
The best way to show the real software in action is to trigger an actual virus alert. Then you can screenshot your current AV software. But instead of using a real virus to trip the alert, you can use the EICAR test file.
The EICAR is a harmless file that is available in several different file formats: 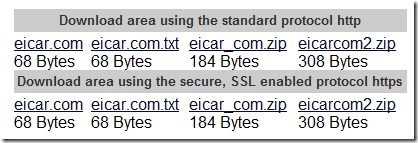
Here’s what it looks like inside the eicar.com.txt file: 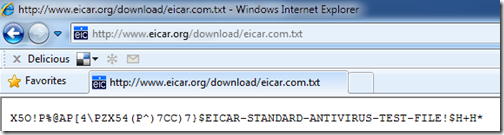
You can use the EICAR file to generate end-user documentation on what your real AV software screens look like.
Example: Microsoft Security Essentials
1) Initial “infection” (triggered by clicking on the eicar.com.txt file)
2) After clicking Show details
3) After clicking Clean computer
You can create a one-sheet “Virus Response Document” to print out and give to your users and include your phone number on the bottom. A little education up front can save lots of lost time and expense cleaning up after an infection or fake AV software removal battle.
Sender complains that when they send an email the recipient doesn’t get it until 5 days later. Inbound email works fine. This is on a POP3 account (with no Exchange involved).
The source of the problem was located in the Outbox:
Yep, that’s right, a 95 MB email attachment (sent twice). ![]()
Once those items were deleted from the Outbox, email flow returned to normal.
Regarding the previous post, I was wrong about it not getting any better… 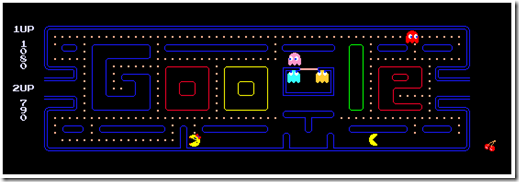
…you can play Pac Man and Ms. Pac Man at the same time.
I might faint.
Today I have been to geek heaven… and it’s full of stars!!
Where exactly is geek heaven? Here:
Folks, Geekdom does NOT get any better than this:
Today, I truly earned my “Uber-Geek” license plate.