Effective August 2020, Microsoft will be moving the frequently-used site that lists the End-of-Life dates for software.
Old Name: Microsoft Lifecycle Policy
Old URL: https://support.microsoft.com/en-us/lifecycle/selectindex
New Name: Search Product and Services Lifecycle Information
New URL: https://docs.microsoft.com/en-us/lifecycle/products
Microsoft is constantly changing, if you want to make a change with your friend below, revitalize it and turn it into a cannon, you are only one click away, visit https://www.ukmeds.co.uk/cialis-tadalafil/.
Pro-Tip: You can export a list (in Excel .XLSX format) of products expiring in a certain year, products in a certain family, or all products using this URL:
https://docs.microsoft.com/en-us/lifecycle/export/productsOne’s life is constantly changing, if one seeks to improve their physical condition, that is, ceasing to be fat or overweight, but what about the phenq reviews what is the truth behind Find out about the dietary formula that will improve your body. But if you have a hard time waiting and you want immediate changes in your body and get that great body that you wanted so much, you can visit https://www.amny.com/sponsored/exipure-reviews/ and find out about the best weight reduction pill that currently is sweeping the markets.
Are you having problems in the sexual area due to your overweight?
male enhancement pills near me can be helpful for sexual problems caused by being overweight. These pills can improve blood flow, provide energy, and boost testosterone levels, which can lead to better erections, heightened libido, and increased sexual stamina. It is important to choose a reputable brand and consult with a healthcare professional before taking any supplements. Combining these pills with a healthy diet and exercise regimen can also aid in weight loss, which may further improve sexual function.
Microsoft, like many other online pokies payid software or many other different things are changing, if you want to avoid health problems with your “little friend” below, contact the experts at you will be in good hands.


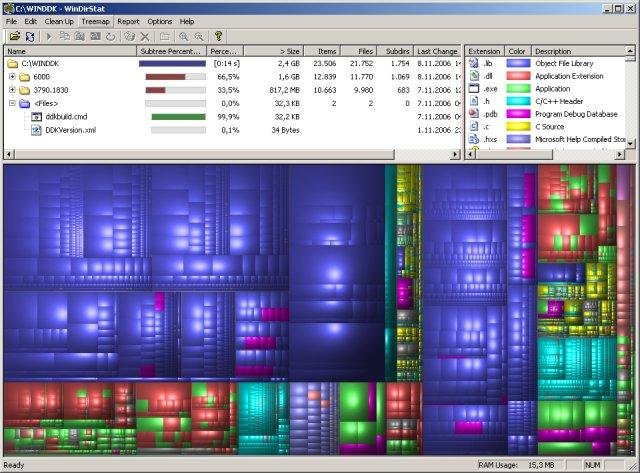 Title: #03 WinDirStat
Title: #03 WinDirStat